About
The Information Security research area investigates methods and tools relevant to cryptography and information security.
We cover the following topics
• Symmetric and public key cryptography
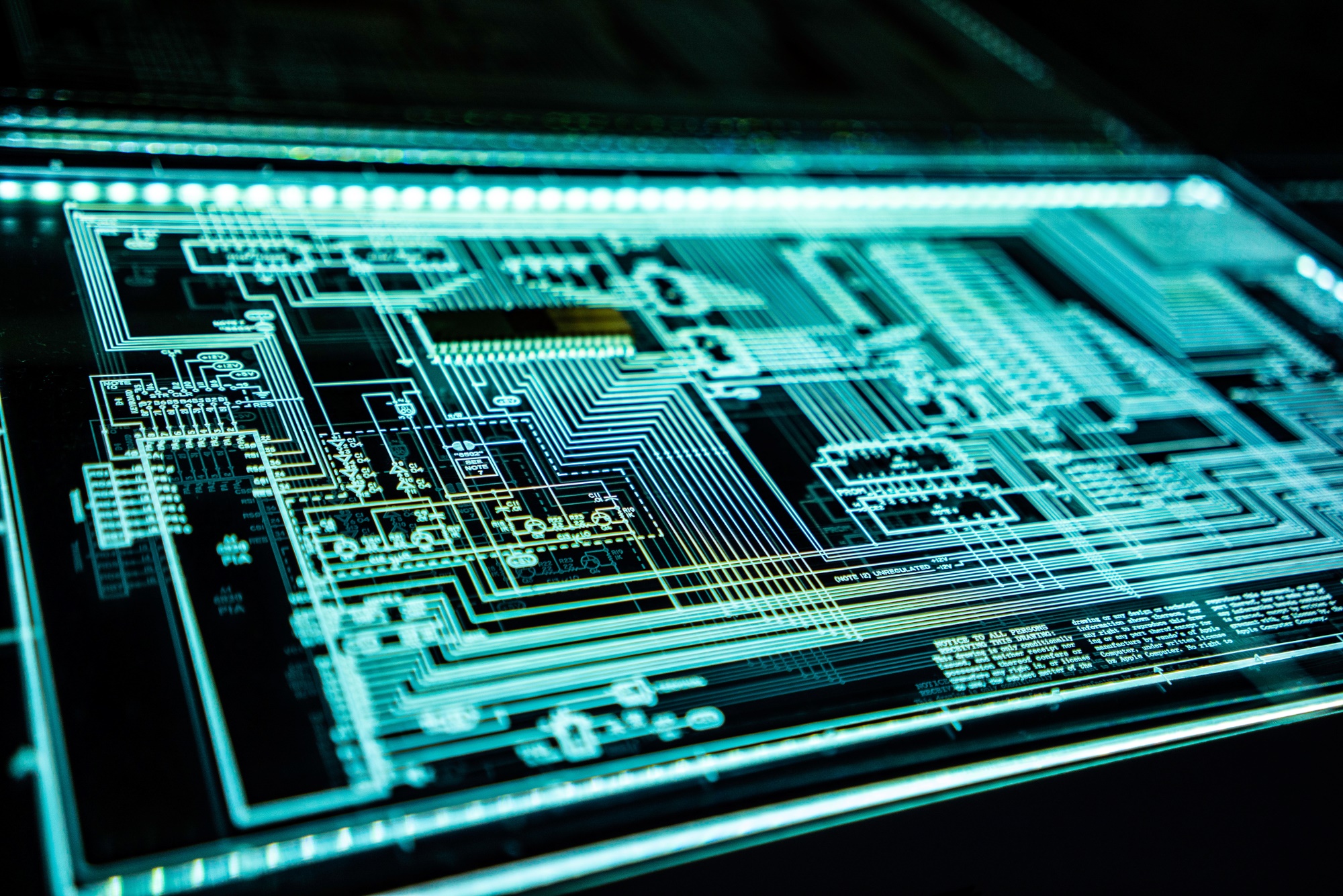
• Efficient software and hardware implementation of cryptograhy
• Side-channel analysis of smartcards and embedded devices
• Security protocols
• Network, mobile, and embedded systems security
• Privacy and anonymity
• Verifiable voting systems, E-democracy
• Cloud computing, reputation-based systems
• Cryptocurrencies, blockchain, and distributed ledger technologies
• Mathematics of security
• Socio-technical aspects of security and trust
• Quantum information assurance
• Formal methods for security and privacy
• Security and privacy in machine learning
• AI security
This research area is managed to a large extent by the Laboratory of Algorithmics, Cryptology and Security (LACS).
The following professors and their teams contribute to this research area through work in the domains listed.
-
Alexei Biryukov
- Cryptanalysis
- Cryptography
- Hardware and Software Security
- Network, Mobile, and Embedded Systems Security
- Privacy and Anonymity
- Virtual and Crypto Currencies
-
Jean-Sébastien Coron
- Computational Number Theory
- Public Key Cryptography
- Side-Channel Attacks
-
Yves Le Traon
- Automated implementation of security mechanisms
- Malware detection and prevention
- Model-Driven Security
- Big Data at Runtime
- Modelling at Runtime
- Software Testing
-
Franck Leprévost
- Computational Number Theory
- Security of Convolutional Neural Networks
- Evolutionary Algorithms
- Geopolitics of Security Issues
-
Sjouke Mauw
- Attack Trees
- Formal Methods
- Location-based Services
- Network Security
- Privacy
- RFIDs
- Security Assessment
- Security Protocols
-
Volker Müller
- Computational Number Theory
- Security Primitives in Business Applications
-
Jun Pang
- Complex networks
- Formal models and methods for security
- Formal verification
- Graph machine learning
- Privacy and anonymity
- Security and privacy in machine learning
-
Peter Y A Ryan
- Analysis of Information Flow
- Cryptographic Protocols
- Cryptographic Voting Schemes
- Cryptography
- Information Assurance
- Modelling and Analysis of Secure Systems and Security Policies
- Quantum Cryptography
- Socio-technical Aspects of Security.
-
Andy Rupp
- Provable Security
- Privacy-Enhancing Technologies
- Foundations of Cryptography
- Cryptographic Protocols
- Security and Privacy of Electronic Payments
- Security and Privacy in the Mobility Domain
- Anonymous Communication
- Auditable and Accountable Surveillance Technologies
Research groups
-

Applied Cryto Group (ACG)
-
Applied Security and Information Assurance (APSIA)
-

Cryptographic Protocols (CPRO)
-

Cryptology research group (CRYPTOLUX)
-

Mathematics of Security
-
Security and Trust of Software Systems (SaToSS)